A Brief History Of Accurate Hacking Scenes In Movies, From 'The Conversation' To 'Blackhat'
Bad hacking is everywhere in movies, but there are a handful of films that actually get it right. The problem is that the good stuff isn't very interesting to look at. Real hackers don't use virtual reality setups, and they don't act like Hugh Jackman in Swordfish. Val Kilmer's line in Kiss Kiss Bang Bang is pretty perfect, even though he's describing being a private detective: "This business, in real life? It's boring."
So we don't see a lot of good hacking on the big screen. Basic terminal windows and UNIX command-line prompts aren't much to look at. But real (or real enough) stuff shows up on occasion, along with other techniques that work in the real world. They include something as simple as guessing passwords (check out the list of the most commonly-used passwords to realize how easy that can be) and go all the way through various forms of social engineering.
After the break you'll find not a ranked list of good hackers, but a chronological exploration of movies that show hacking as it is in real life. (Kind of.) What you'll see is that the good film hackers are pretty consistent, and haven't changed much through a few decades of filmmaking.
 The Worst Examples
The Worst Examples
First, let's get the bad stuff out of the way so you know what we're not talking about. You can throw a rock and hit six bad hacking scenes from movies and TV, but my personal terrible favorite is a scene with an evil hacker mastermind played by Eric Bogosian in Under Siege 2. He seems to understand something about RAM that the rest of us have totally missed. Watch the scene:
How does anyone write that? Screenwriters aren't dumb, and they can at least consult sources to make sure that the scenes they're writing are somewhat accurate. There's always the chance that someone else can dumb down any given scene, but there's another option, too. Maybe at times the really bad stuff is intentional.
Here's a Reddit post claiming to be from a writer with experience on CSI:
We write those scenes to be inaccurate and ridiculous on purpose. I'm a young writer in his mid-30's, computer and game savvy. Lots of us are. I guess you could call it a competition of one-upping other shows to see who can get the best/worst "zoomhance" sequence on the air. Sometimes the exec producers and directors are in on it, and other times we just try to get bits and lines into scripts. 90% of our TV viewing audience will never know the difference and honestly, we love it when threads like this get started and love reading the youtube comments.
That's an anonymous post, so giving it too much weight isn't a good idea. But having spent a lot of time working as a props guy and set dresser, I do know that art departments make things fun for themselves whenever possible by adding background details to keep the day feeling lively. I can believe that some writing staffs, especially for shows like NCIS and CSI, might do the same thing.
In this list rundown of terrible hacking, you'll see some of that in action. Bonus points here for using yet another scene from Under Siege 2.
And then there's the all-90's version.
***
OK, enough of the lousy stuff. Let's get to the films that have some legit hacking in them. Sadly, there aren't many.
 The Conversation (1974)
The Conversation (1974)
You're wondering what a 1974 movie has to do with hacking, and it's true, there's no computer hacking here. But hacking is really just a specific form of electronic data collection, and that's what Gene Hackman's character Harry Caul does — he just uses analog tech rather than digital.
The film also features a really good detail that points to the very origin of hacking. One of Harry Caul's rivals demonstrates a device that blows a specific tone into a phone system, which converts the phone on the other end of the line to a microphone. That's related to phone phreaking, which is where hacking was born.
One of the coolest bits of phone phreaking history is that some of the most proficient early phreaks were blind. In fact, the earliest was Joe Engressia, who legally changed his name to Joybubbles, a boy born blind and with perfect pitch. At five years old he discovered that tapping a specific pattern with a phone's switch hook could trick the phone system into action. Soon, he could whistle a 2600Hz tone into the phone, which tricked the tone-based phone system into activation. (Much like the device in The Conversation.) Other notable phone phreaks include Steve Jobs and Steve Wozniak.
As phreaking developed into the '70s, enthusiasts built electronic boxes to simulate other tones and help control phone systems. Some of that tech is for sale in the trade show attended by Harry Caul in The Conversation. (Thanks to my friend Dan for suggesting this entry. There's a good essay on the intersection between The Conversation and phone phreaking here.)
***
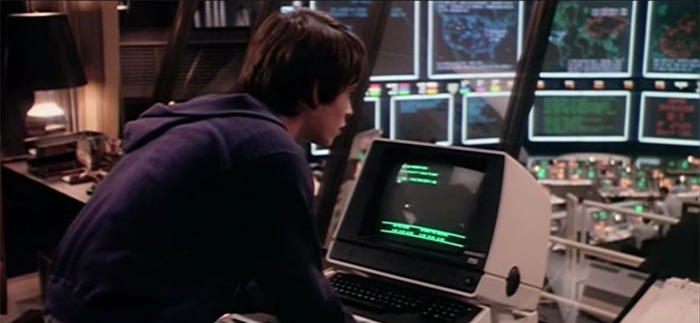
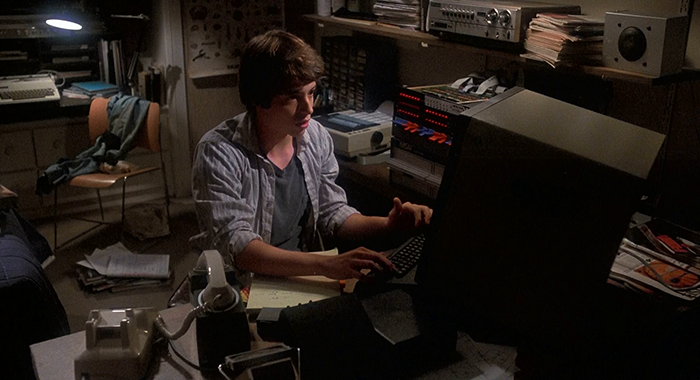 Wargames (1983)
Wargames (1983)
Matthew Broderick plays David, a kid with a computer and a lot of time on his hands. This kid isn't evil, just curious. He uses his relatively rudimentary modem to explore computer networks just for fun, at one point looking for info on upcoming video games. During one bulk scan of phone numbers, David stumbles on a computer that is a bit different. His interest piqued, David soon finds his way into a system that belongs to NORAD — aka the North American Aerospace Defense Command.
Some of the most legit hacking in the film is actually David's research on a specific topic once he has had his first access to WOPR, the computer at NORAD. David is on the hunt for a backdoor password that will allow him invisible access to the system. So he kicks into a version of social engineering, using clues in the part of the system he was able to access to get external information about its designer, and ultimately guess the backdoor password. The password isn't as simple as one of the dumb ones in the "most popular passwords" list we mentioned before, but the film is a good example of how someone trying to break into a system might first go about it.
Perhaps the funniest part of Wargames is that, while David sets the film's plot in motion by searching for information about video games, he's really not a particularly good gamer. Big points for the hacking, though. (Broderick would reprise his hacker origins to a certain degree in Ferris Bueller's Day Off.)
***
 Sneakers (1992)Sneakers has some embellished hacking, sure — an all-powerful MacGuffin box drives the plot — but it also has some really good examples of basic real-world hacking concepts that take place away from the computer. Robert Redford's character runs the sort of legit hacking that earns big money for talented practitioners, testing the systems of various companies for potential security flaws. They do the sort of reconnaissance that we typically see in heist movies, looking up blueprints for a facility they need to penetrate, and they use various forms of social engineering to acquire an access key. There's a good rundown of some of the techniques in the film here.
Sneakers (1992)Sneakers has some embellished hacking, sure — an all-powerful MacGuffin box drives the plot — but it also has some really good examples of basic real-world hacking concepts that take place away from the computer. Robert Redford's character runs the sort of legit hacking that earns big money for talented practitioners, testing the systems of various companies for potential security flaws. They do the sort of reconnaissance that we typically see in heist movies, looking up blueprints for a facility they need to penetrate, and they use various forms of social engineering to acquire an access key. There's a good rundown of some of the techniques in the film here.
The characters even go dumpster-diving to find documents. Dumpster-diving was a big part of the early phone phreaking scene, too, as early phreaks raided discarded phone company documents to get insider information on how phone networks were assembled. It's not as glamorous as using garish 3D cube models to represent some bizarre virtual space, but it's a trick that gets the job done.
And as he has pointed out multiple times, Sneakers is (or was, a couple years ago) the favorite hacking movie of famed real-world hacker Kevin Mitnick. That's about as good an endorsement as you need.
***
The Matrix Reloaded (2003)
What, no The Matrix? Well, the original film captured some of the then-current interest in hacking, and used it as a portal to a philosophical sci-fi story. Most of the "hacking" in the Matrix films, however, is just more rapid finger tapping and random code gibberish. But The Matrix Reloaded sees Trinity using a real-world tool called Nmap, and the scene is popular enough that it has pages dedicated to explaining the intersection between the scene and reality.
So what's going on in that clip? A reddit comment explains it better than I can:
At :03, you can see at the top she scanned (Nmap) a server and noticed it had SSH running, which is used for administering computers remotely. She then uses sshnuke, which is a program that exploits SSH and resets the administrative password that she sets (Z1ON0101). Then she logs in as administrator using that password. Then once she's in, she just executes a command that disables the grid nodes.
Usage of Nmap is popular enough in films that the official Nmap page has a whole collection of screens and explanations for the tool as used in past and, in some cases, far future storylines. It shows up in Dredd, Elysium, The Bourne Ultimatum, and the original The Girl With the Dragon Tattoo, among others.
***
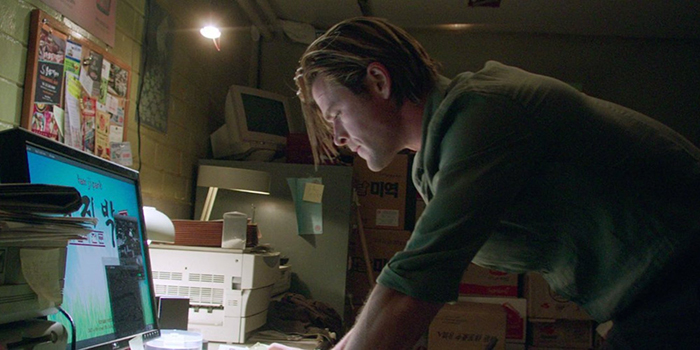 Blackhat (2015)
Blackhat (2015)
Go ahead and laugh at Chris Hemsworth playing an MIT hacker, but many of the little details are just right in Michael Mann's latest film. That's no surprise given Mann's preoccupation with detail, but it is a pleasant surprise given the fact that Blackhat blows it with some other details. And yet none of it is new. While films of the '90s were all about pushing the idea that technology is an outlandishly visual new frontier, the best hacking movies and scenes approach the subject in the same way we've seen for decades.
Hemsworth's character Nick Hathaway uses quite a few real-worlds tricks to gain access to systems. A couple of the most attention-getting bits in the film isn't something that most hackers would do — they involve extreme violence and a crashed car — but in general the type of threat faced by the characters is quite legit. Indeed, the threat seems kind of boring to some audiences, as the bad guys are targeting a utility in order to make money. But cyber-terrorism does go after such targets just as often as it angles towards a company like Sony.
There's also a big example of social engineering rendered with terrific detail, as a woman persuades a security guard to connect a USB flash drive to his company's system, allowing Hathaway to have access. And this film looks right when it comes to hacking, as we see Hathaway typing away at UNIX-based systems with the same command lines everyone in the real world uses.
Wired showed the film to a set of "200-odd security specialists from Google, Facebook, Apple, Tesla, Twitter, Square, Cisco, and other parts of Silicon Valley's close-knit security community," and found afterward that the audience generally endorsed the legitimacy of many of the tactics used.